By Connor Walsh, CISSP, and Jane Lacson, CCE, CHTM
 With the influx of cybersecurity-related incidents over the past several years, corporations find themselves budgeting and deploying layers upon layers of physical, technical and administrative controls to protect their critical assets. From building state-of-the-art server rooms, to installing top-of-the-line firewalls and rolling out policies to maintain long-term compliance, defense in depth strategies with this level of complexity should be impossible to penetrate. So, how are hackers consistently able to breach them? Unfortunately, every organization has the same weakest link that can be compromised repeatedly – employees.
With the influx of cybersecurity-related incidents over the past several years, corporations find themselves budgeting and deploying layers upon layers of physical, technical and administrative controls to protect their critical assets. From building state-of-the-art server rooms, to installing top-of-the-line firewalls and rolling out policies to maintain long-term compliance, defense in depth strategies with this level of complexity should be impossible to penetrate. So, how are hackers consistently able to breach them? Unfortunately, every organization has the same weakest link that can be compromised repeatedly – employees.
Security awareness training within an organization is extremely important and is, unfortunately, a concept that is sometimes overlooked. As members of healthcare technology management (HTM), we have a unique opportunity to provide some of this security awareness during environment of care rounds. Consider asking different questions to the clinical staff that directly correspond to your internal cyber-related policies. Examples include, “Do you know who to call in the event of a medical device cyber incident?”, “Do you ensure vendor USBs are scanned prior to being plugged into any medical device?” and “If a vendor comes to your area without HTM knowledge, do you keep a detailed log of their contact information?” Ingraining this security mindset in your facility’s clinicians can help prevent, or mitigate, any potential cyber event.

 Social engineers psychologically manipulate people into gathering sensitive information or access to valuables. They have many techniques to get the information they want, but one of the most prevalent is phishing. Phishing is getting more sophisticated and has become one of the top cybersecurity threats for data breaches. The most common types of phishing tactics are displayed in Figure 1.
Social engineers psychologically manipulate people into gathering sensitive information or access to valuables. They have many techniques to get the information they want, but one of the most prevalent is phishing. Phishing is getting more sophisticated and has become one of the top cybersecurity threats for data breaches. The most common types of phishing tactics are displayed in Figure 1.
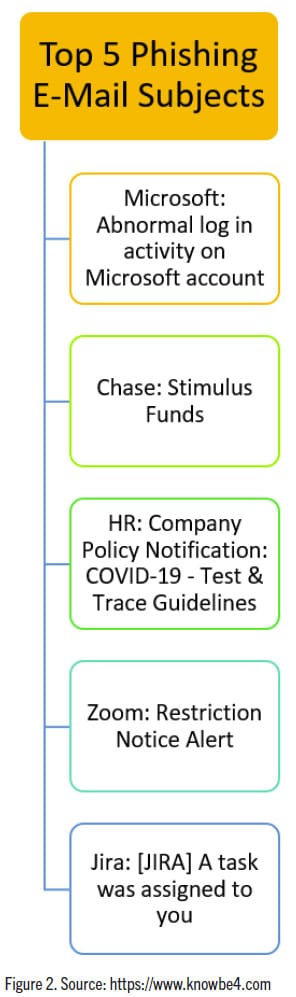
Like a fisherman, the bait and tactics are ever evolving to ensure the highest yield. As a recent example, COVID-19 was a hot topic that was quickly seized upon. Attackers mimicked the CDC sending e-mails, texts and calls to potential victims with links about testing which would install ransomware and malware on a computer. When shortages of PPE happened, there were attacks that stated “Click this link to get your mask tomorrow!” The new phishing attempts are focused on the COVID-19 vaccine. There will be a plethora of e-mails, texts and calls with links to click on in an attempt to try and get the vaccine. Some will bait you on cost, some will bait you on availability but don’t fall for it. You can’t pay to put your name on a list or get early access; no one that is legitimately offering the vaccine will ask you for your social security, bank or credit card number. There were roughly 2,500 domain names registered with the word “vaccine” since November 2020. These sites will hype up desperation and urgency to try and get you on a list or pay this amount now to get the vaccine. As health care workers, you are on the frontlines and it is best to report these scams to your information security officer. Figure 2 highlights some common phishing emails currently being used.
Our lives and the world around us are fully integrated into technology. More and more advancements happen on a daily basis to keep us informed and connected. Cybersecurity and privacy are a huge issue on this front and attacks will continually happen to get information. Data sells. Your data needs to be protected as best as possible. Phishers become more sophisticated in their attacks, but you can be proactive about it. Take cybersecurity training, put yourself through a phishing simulation, trust your instincts if something looks suspicious and be wary of who is asking for sensitive information. Don’t be afraid to send it in for another level of review. No one will ever fault you for being too cautious or wanting to maintain a high level of security. As Frank Abagnale said, “Hackers do not cause breaches, people do. A breach happens because an employee did something they weren’t supposed to do or because an employee didn’t do something they were supposed to do.”
Connor Walsh, CISSP, is a supervisory clinical engineer for the VA Boston Healthcare System.
Jane Lacson, CCE, CHTM, is the supervisory biomedical engineer at the Veterans Health Care System of the Ozarks.
The views expressed here are those of the author and do not necessarily represent or reflect the views of TechNation or MD Publishing.




