Sponsored by Nuvolo
 By Tony Bailey
By Tony Bailey
 In some health care organizations, there are two departments who don’t always sit at the same table. The healthcare technology management (HTM) team who support the medical devices, and the IT security team who responds to security events. The technicians in the HTM team are responsible for device safety and the IT security analysts protect information.
In some health care organizations, there are two departments who don’t always sit at the same table. The healthcare technology management (HTM) team who support the medical devices, and the IT security team who responds to security events. The technicians in the HTM team are responsible for device safety and the IT security analysts protect information.
When there’s insufficient collaboration between these teams, device disruption due to security events can take too long to remediate. Adverse patient outcomes or data loss can then occur.
It’s not that there’s no one monitoring for unusual device activity. Medical device discovery and security vulnerability tools do an excellent job. They monitor networks and identify devices with vulnerabilities and create security notifications. They’re also able to provide information about the devices’ network information like IP and MAC address and, in some cases, an assessment of the cyber security risk.
But the HTM and security teams need to ensure there’s a coordinated, quick remediation process that scales to hundreds of devices. Without this, device safety and a health care organization’s reputation can be put at risk.
But this coordination can get bogged down when device information is stored across legacy software applications, documents and spreadsheets. With no common data fields or standardized data across multiple device inventories, it can take way too long even to find a device owner’s name.
 The first step to achieve fast remediation is a single source of truth of device inventory. You can’t protect a device without a full device lifecycle profile from purchasing through to retirement. This single trusted data store should contain not only device hardware and software profiles but also the latest device usage information, last known location and the device owner’s name. And every time a device undergoes routine planned maintenance, or a corrective maintenance work order, the device information in this single inventory gets updated.
The first step to achieve fast remediation is a single source of truth of device inventory. You can’t protect a device without a full device lifecycle profile from purchasing through to retirement. This single trusted data store should contain not only device hardware and software profiles but also the latest device usage information, last known location and the device owner’s name. And every time a device undergoes routine planned maintenance, or a corrective maintenance work order, the device information in this single inventory gets updated.
With a single inventory, combined with discovery and monitoring tools data, the security and HTM teams can get a shared view of device profile data and security event data in an “intelligence hub.” When unusual activity is observed for a device, the security team can see what the device is, the owner, location, last maintenance date and the latest software information.
And this is where the fast remediation comes in. It’s probably the most important part of device cyber security. After all, getting alerts is one thing. Acting on them quickly with full visibility to all concerned is another.
The intelligence hub is built on a platform that orchestrates and automatically initiates remediation workflows. This workflow automatically creates a work order to dispatch HTM resources to respond and correct the affected device before it can impact patient care.
As a result, a health care organization can operate devices that are less open to disruption, improving patient safety. With the intelligence hub, the HTM team and security teams have accurate visibility into detailed device information such as location, software and firmware upgrades or a manufacturer recall.
Nuvolo OT Cyber Security creates an intelligence hub consisting of a single trusted data store of device information integrated with security events from device monitoring solutions like Medigate, Ordr, Asimily, Cynerio, Palo Alto Networks, CyberMDX and many others. The device data store replaces the multiple inventories and device records with a single SaaS-based solution. Nuvolo OT Cyber Security helps optimize safety, accessibility and availability by providing context and correlation of security events across all devices. When a security event occurs, the security team not only knows who to contact, but they can also prioritize the response based on threat risk and the number of devices affected.
Running on Nuvolo initiates a workflow to orchestrate an automated response that includes work orders to dispatch an authorized HTM resource to respond and work on the affected devices. This response approach includes device tracking and ticketing so that the security team has a real-time status on the response progress.
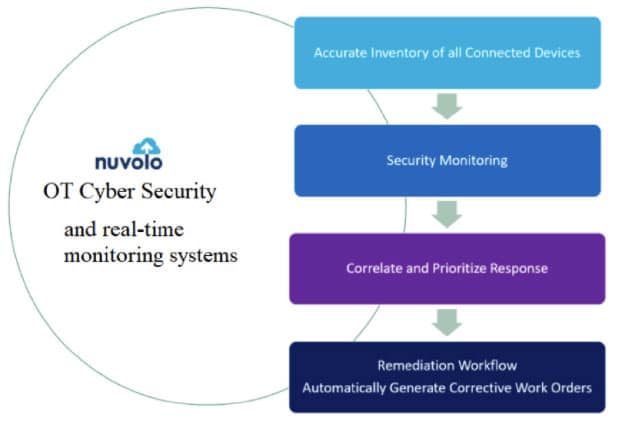
Nuvolo OT Cyber Security enables this seamless approach of people, process and technology to accelerate remediation. This approach helps improve quality and safety when device cyber security events occur. Nuvolo OT Cyber Security capabilities achieve the steps needed to ensure a strong cyber security posture, including:
- Single device inventory
- OT device monitoring when deployed with supporting third-party monitoring services
- Pre-integrated vulnerability data sources that leverage National Institute of Standards and Technology (NIST) Common Weakness Enumeration (CWE), Common Platform Enumeration (CPE) and Common Vulnerabilities and Exposures (CVE) vulnerability data imports. And, matching of documented vulnerabilities from NIST/MITRE Corporation
- A rules-based identification algorithm that identifies the device or devices that are affected by the event or vulnerability. And, the security context and impact of the event including what patch, configuration change or mitigating controls are required to then determine the remediation priority
- Orchestration of the next steps, including kicking off remediation workflows to generate a work order
For more information about Nuvolo OT Cyber Security to enable your health care organization to have a single device inventory, device monitoring and orchestrated remediation for security events, visit https://www.nuvolo.com/solution/cyber-security/.
Tony Bailey is the director of product marketing for Nuvolo OT Cyber Security.




