By ECRI
Four Steps for Securing an Infusion Pump Wireless Network
Infusion pumps can be critical to the treatment of patients throughout a health care facility – which is why the security of the infusion pump network demands careful attention. A single malfunctioning pump can be promptly replaced. But a security incident that impacts multiple networked pumps or that spreads to other networked systems, as in the case of a ransomware outbreak, could severely impact a health care organization’s ability to provide care.
Infusion pumps deliver medications or other fluids – sometimes life-sustaining ones – with high accuracy over a specified time interval. While pumps may be used in a stand-alone configuration, increasingly they are integrated as part of a network. “Integration offers several benefits,” notes Juuso Leinonen, a principal project engineer in ECRI’s device evaluation group. “Features like autoprogramming, automatic documentation of infusion parameters in the patient’s EHR, and remote drug library updating can improve patient safety and workflow.”
These benefits, however, depend on wireless coverage that is pervasive, responsive and secure in all areas where pumps are used. Disruptions to the wireless network – whether through a security incident or some other cause – could adversely impact the delivery of care. To secure infusion pumps that are integrated as part of a network, ECRI recommends the four steps outlined below.
1. Establish a Unique Wireless Network
In terms of number of units, infusion pumps are the most common medical device on a hospital network. To simplify implementing security controls for such a large number of devices, facilities should establish a separate Service Set Identifier (SSID), or wireless network, exclusive to infusion pumps. The pumps on that network should have similar configurations and interact with the same servers.
Additionally, client isolation – the clients in this case being the infusion pumps – can be enabled on the SSID. This measure restricts infusion pumps from transmitting network traffic to each other; thus, it can prevent a compromised pump from affecting other pumps on the same subnet.
2. Use Security Controls to Isolate and Protect the Network
Most network traffic involving infusion pumps should be to and from pump servers. For example, pumps receive infusion orders from the server, and the server receives status information from the pumps. The pump server may also interface with components like the EHR (to receive medication orders and send status information), drug library software (to update medication protocols) and possibly an external server hosted by the pump vendor (to perform data analytics).
Pump server access should be controlled with a role-based access control (e.g., Active Directory) that specifies authorized activities for different roles (e.g., health technology management personnel can download logs, pharmacy personnel can modify drug libraries). Physical access to the pumps themselves is not normally controlled because of the challenges such control would pose to normal clinical workflow, although passcodes or passwords may be deployed to limit unauthorized access to certain settings and to prevent tampering.
Firewalls or access control lists (ACLs) should govern the traffic to and from the infusion pumps on the wireless network. Pumps should only be able to access servers necessary for their function. In most cases, that should be limited to pump servers. Pumps do not require direct access to the Internet.
This practice, called network segmentation, helps reduce the impact of a cyberattack. Chad Waters, a senior cybersecurity engineer in ECRI’s device evaluation group, explains: “Segmentation helps in both directions. It limits which hosts can reach a device (and attack it). And in the event that a device is compromised, segmentation helps contain the attack to prevent a wider outbreak.”
Additionally, network access control (NAC) systems can be used to provide more robust control over device access to the wireless pump network. Also, internet of medical things (IoMT) security solutions – systems that analyze network traffic – can aid in device inventory and discover security issues.
3. Implement Strong Wireless Security Settings
Wireless security standards provide methods for client authentication, which is the process of proving a user’s identity, and traffic encryption, which is a process that makes data unreadable or unusable by an unauthorized party. ECRI recommends implementing the strongest wireless security standard that is compatible with infusion pump systems. For most current implementations, that will mean using the WPA2 Enterprise wireless security standard.
WPA, which stands for Wi-Fi Protected Access, is a family of modern encryption and authentication protocols, with separate versions developed for Personal and for Enterprise settings. (Personal versions of the WPA standards are not appropriate for facility-wide implementations.) The original WPA standard was depreciated – that is, retired – in 2012 and should not be implemented; it includes security vulnerabilities that could be exploited. WPA2 Enterprise is now in common use and is well supported by infusion pump manufacturers.
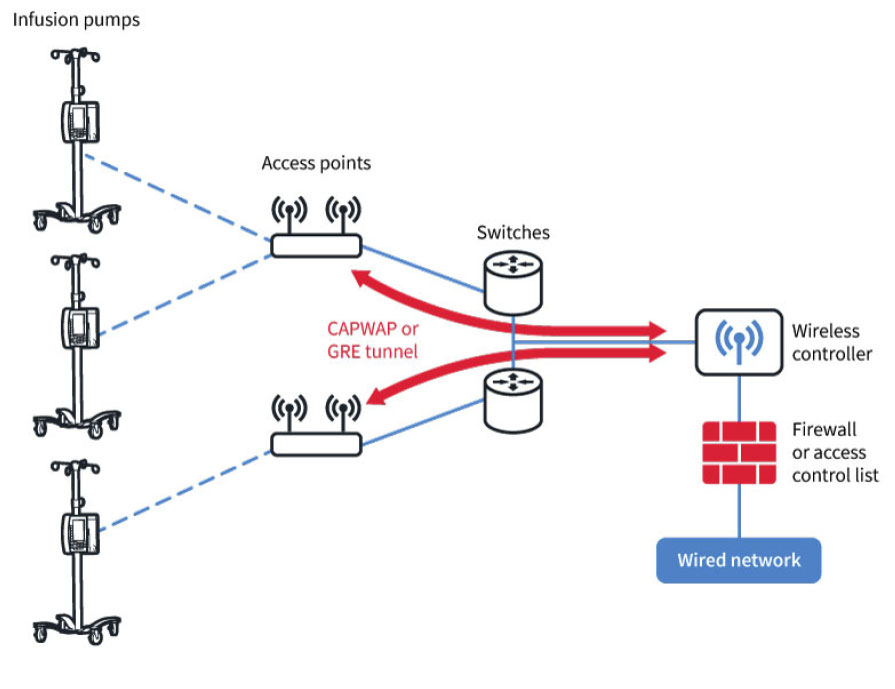
WPA3, on the other hand, which was certified as a standard in 2018 and offers many upgraded security features, is not yet well supported. Although several common operating systems introduced support for WPA3 by the end of 2020, introducing WPA3 support into infusion pumps may take much longer. In the meantime, you may want to consider laying the groundwork for WPA3 as you wait for infusion pumps to support it; that effort might include upgrading your wireless infrastructure, including the access points and any wireless controllers (servers).
4. Maintain Your Infusion Pump and Wireless Systems
All components of the infusion pump network need to be properly maintained to prevent security incidents. That includes not only the pumps and pump servers, but also the wireless system and other supporting network infrastructure, such as the wireless controllers, access points, and any security controls like firewalls or NACs. The goal is to reduce the risk of the wireless network itself becoming an entry point into the system.
For pumps and pump servers, firmware updates and patches should be tested on a subset of pumps. The rest of the inventory should then be updated according to a schedule dictated by the priority of the update. It may be possible to perform low-priority updates during routine preventive maintenance, but more severe security concerns should be remediated more quickly.
To Learn More . . .
This article is adapted from ECRI’s Guidance Article, “Best Practices for Securing an Infusion Pump Wireless Network” (Device Evaluation 2021 May 19). The complete article is available to members of ECRI’s Capital Guide, Device Evaluation, and associated programs. To learn more about membership, visit www.ecri.org/solutions/evaluation-and-comparison, or contact ECRI by telephone at (610) 825-6000, ext. 5891, or by e-mail at clientservices@ecri.org.




