 Cybersecurity remains a hot topic in the healthcare technology management (HTM) world. In a December 2022 cohort study of 374 ransomware attacks, the annual number of ransomware attacks on health care delivery organizations more than doubled from 2016 to 2021, exposing the personal health information of nearly 42 million patients. During the study period, ransomware attacks exposed larger quantities of personal health information and grew more likely to affect large organizations with multiple facilities.
Cybersecurity remains a hot topic in the healthcare technology management (HTM) world. In a December 2022 cohort study of 374 ransomware attacks, the annual number of ransomware attacks on health care delivery organizations more than doubled from 2016 to 2021, exposing the personal health information of nearly 42 million patients. During the study period, ransomware attacks exposed larger quantities of personal health information and grew more likely to affect large organizations with multiple facilities.
The study results suggest that ransomware attacks on health care delivery organizations are increasing in frequency and sophistication; disruptions to care during ransomware attacks may threaten patient safety and outcomes.
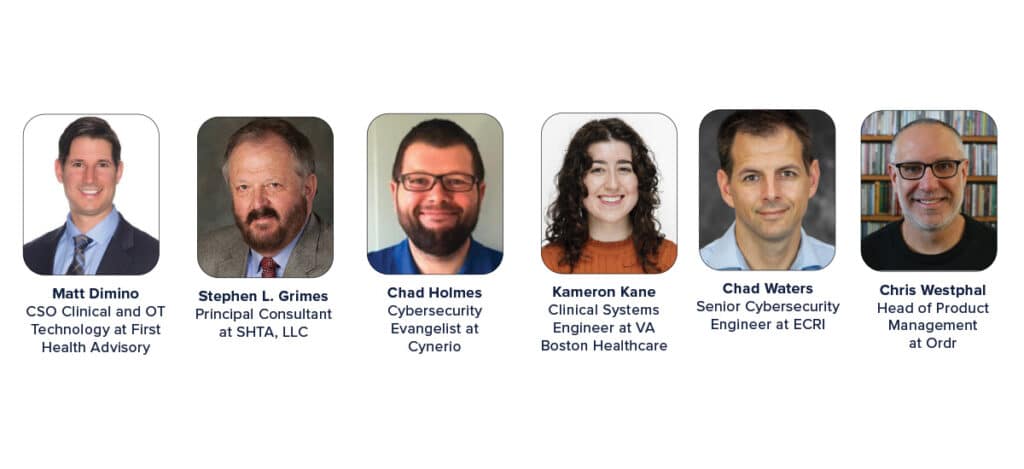
TechNation reached out to experts in the field to shed more light on cybersecurity. Participating in the roundtable are First Health Advisory’s CSO Clinical and OT Technology Matt Dimino, CISM, CRISC, HCISPP; Strategic Healthcare Technology Associates LLC Principal Consultant Stephen L. Grimes, FACCE, FHIMSS, FAIMBE, AAMIF; Cynerio Cybersecurity Evangelist Chad Holmes; VA Boston Healthcare System Clinical Systems Engineer Kameron Kane; ECRI Senior Cybersecurity Engineer Chad Waters and Ordr Head of Product Management Chris Westphal.
 Q: What are three basic things an HTM department needs to do in regard to cybersecurity?
Q: What are three basic things an HTM department needs to do in regard to cybersecurity?
DIMINO: HTM staff members need to understand the departmental and organizational objectives and have a basic strategy with structure. HTM leadership should work with security leaders to map out security requirements and define the limitations and expectations through a form of governance. HTM leadership should also draw up the department roadmap and share appropriately with their frontline staff. Learn to bake cybersecurity practices into routine operations, such as evaluating and populating network and security attributes in the CMMS during PMs and CMs. This requires data governance around the expectations for network and security data within the CMMS. Don’t overpopulate with data just because you can; it’s not helpful if you don’t know why you need it. Also, track technician efforts with work orders and codes; this helps support long-term initiatives with metrics and measures the level of effort, which can support the need for additional staff or professional services. Budget for training just as you would for OEM or ISO equipment-specific training. Numerous organizations offer various flavors of cybersecurity training including self-paced and boot camps. Not all training should be technical as some staff members need to understand risk and how risk is measured and articulated to leadership.
Grimes: CE/HTM services and their staff should:
Familiarize themselves with cybersecurity issues (i.e., read relevant articles & take relevant courses so they understand both cybersecurity in general as well as unique issues associated with medical device cybersecurity).
Familiarize themselves with their organization’s current approach to cybersecurity and the extent to which the organization’s current cybersecurity program takes into consideration the cyber vulnerabilities and risks associated with medical technology.
Work with the organization’s IT security professionals, manufacturers and other key stakeholders to insure the organization’s seamless and comprehensive approach toward cybersecurity risk management.
Establish who is going to be responsible for various security program elements and insure they are executing their role. Conduct tabletop exercises with various stakeholders for training purposes and to determine whether everyone is prepared.
Holmes: Improving cybersecurity practices within HTM teams is a combination of improving human practices and effectively adopting technology. Among the top steps teams can take are:
Improve Communication with Colleagues: The most effective HTM teams have strong relationships with their IT, Security and Network peers. Unfortunately, this is often an exception, resulting in cybersecurity challenges caused by lack of staffing, miscommunication and ticket-driven communications. Improving how HTM teams work with their colleagues is critical in most environments.
Clarity in Guidance: HTM teams spend significant amounts of time attempting to work. From searching for devices to understanding where to download patches, time is frequently wasted in clarifying device-level actions. By providing clarity in requests, resources, guidance and device details, HTM teams can see improvements in both efficiency and implementing cybersecurity protections.
Prioritization of Actions: Cybersecurity products are notorious for overloading teams with numerous findings. HTM teams should explore systems that allow them to not only understand actions, but also automatically prioritize and act on those findings based on the actual risks they represent. Products using standard scoring systems like the Common Vulnerability Scoring System (CVSS) to determine severity, and the Exploit Prediction Scoring System (EPSS) to measure likelihood are proving to be the most effective scoring approaches for prioritizing action.
Kane: It’s safe to say HTM departments are familiar with the power of preventative measures, and cybersecurity is no different. One small action item is simply installing antivirus software on as many devices as possible. Scaling up, maintaining an accurate inventory of all networked medical devices is imperative to the security of your department. Finally, when cybersecurity incidents do arise, having an established reporting and response plan in place is best practice. The goal is to diminish administrative time that should be spent addressing the incident at hand.
Waters: The most important thing is to maintain a complete inventory with relevant data points including firmware versions and network addressing – you need to know what you have in order to protect the environment. My two other suggestions are related to procurement and maintenance respectfully. A security assessment should be a formal part of the purchasing approval process. For technology already in place you should develop a medical device security policy to proactively reduce security risks and manage ongoing security concerns.
westphal: An HTM department should do the following three basic things in regard to cybersecurity:
Establish a method to ensure a complete, up-to date inventory of all assets under management with comprehensive and accurate asset details. Inventory tools such as a CMMS and/or CMDB provide a central repository for asset information and methods that leverage automation can ensure that all connected assets are included with up-to-date, comprehensive and accurate details.
Establish methods to identify and address asset vulnerabilities. This includes identifying assets with outdated and unpatched operating systems and software that is not up to date or should not be installed.
Establish relationships and workflows with your counterparts on security operations teams to share insights and best practices, coordinate incident response efforts, and collaborate on proactive measures to improve protections.
Q: What are some of the latest threats and preventative measures health care facilities should be aware of in 2023?
DIMINO: Threats will always be imminent; therefore, don’t plan for specific threats; plan for iterative risk management practices by understanding how to reduce and respond to risk efficiently and effectively. Devices may not be specifically targeted, but they are prime candidates for lateral movement which will be debilitating since most are unpatched, unsegmented and unmonitored. Preventative measures include hardening devices during onboarding by having risks appropriately identified, addressed and tracked. A true life cycle approach is necessary, and the best way to accomplish this is by creating a program with policies, procedures, guidelines, metrics, governance and senior leadership support.
Grimes: The reality is that medical devices and systems continue to evolve and, consequently, will invariably contain unsecured and unprotected elements that are vulnerable to a growing number and variety of security threats. These cybersecurity threats may come in the form of ransomware, state-sponsored cyber-attacks, or malicious assaults where medical technology may or may not have been the original, intended target. Health care facilities will need to constantly evaluate their evolving systems to understand where system vulnerabilities are occurring. Those health care facilities also need to monitor the growing variety of threats to insure they are taking appropriate steps to inoculate their technical system vulnerabilities from these threats. Such “inoculation” may involve regular software updates, user education, password management, anti-malware applications, firewalls as well as other administrative, technical and physical safeguards.
Holmes: The Bad News: Insecure and unpatched IoT/IoMT deployed on unsegmented networks will continue to be primary attack vectors for phishing, ransomware, malware and related attacks for the foreseeable future. Many attacks on health care aren’t elegant, but instead take advantage of insecure environments to spread rapidly before compromising multiple systems.
The Good News: Many of the challenges seen in health care have well-known protections in industries considered to be leaders in cybersecurity adoption (finance, insurance, commercial, etc). Properly segmenting networks to prevent cyberattack spread, improving patch management effectiveness, and adopting modern approaches to detecting and responding to attacks can quickly improve the security posture of the vast majority of health care organizations.
Kane: As supported operating systems shift away from infrastructure greater than 10 years old, legacy machines create huge cybersecurity gaps. Medical device manufacturers face a unique compatibility obstacle, weighing the requirements of medical software against operating systems that update on a much quicker timeline. Although HTM departments themselves cannot produce software as quickly as they may need it, knowing your unsupported devices creates the foresight to upgrade when possible.
Waters: Ransomware isn’t going anywhere because the primary motivation for malicious hacking is financial – extorting organizations by withholding access to critical data or IT functions. While medical devices may not always be the primary target, they can be impacted when the systems that support them go down. HTM departments should be prepared for those situations by having backup plans and downtime procedures for every device type.
westphal: Ransomware continues to be a top threat to health care facilities in 2023. Knowing your attack surface (i.e., the assets connected to the network) and the potential threats (i.e., vulnerabilities and risky communications) is an essential first step to protecting your environment from the impact to ransomware. Ensuring operating systems and software packages are up to date and patched will eliminate known vulnerabilities that an attacker can exploit. Assessing network communications helps to identify devices that are deployed in the wrong part of the network (e.g., medical devices connected a guest network) in addition to vulnerable protocols (e.g., RDP, FTP, Telnet, and SMB) that should be disabled or restricted. Identifying and restricting Internet facing communications is also an important step. Internet communications that are unnecessary or potentially malicious (e.g., to known malicious sites or to domains in high-risk geographies) should be blocked at perimeter controls such as firewalls. Network segmentation is another measure that can limit the attack surface and reduce risk for systems where patching is not an option. Segmentation can be applied at a broad level to restrict communications among a group of assets (e.g., an emergency room, ICU, or NICU) or at a granular level to allow only specific communications to and from a specific asset.
Q: Can you tell us about one technology, product or service biomeds can use to help protect a facility?
DIMINO: This combines IoMT passive scanning solutions, your CMMS, and professional services. Tools alone won’t solve the problem as these require people and processes to support. Medical device security is hard, inefficient, expensive to build internally, and is often disjointed when you attempt to buy different tools to support the security initiatives. First Health Advisory offers professional services that will help operationalize and integrate these tools which will accelerate the value and demonstrate ROI.
Grimes: In recent years, a number of services and products have been developed to aid CE/HTM professionals in the management of cybersecurity risks. The Association for the Advancement of Medical Instrumentation (AAMI) has published “Medical Device Cybersecurity: A Guide for HTM Professionals” that offers advice from 25 industry experts on how CE/HTM professionals can implement an effective medical device cybersecurity program within their organizations. AAMI also offers a 6-plus hour online course on “Medical Device Cybersecurity 101 for HTM Professionals” that is taught by industry experts and includes a copy of the aforementioned guide and covers it key program elements. Several companies (e.g., Asimily, Medigate) have produced software tools designed to help identify, manage and mitigate medical device cybersecurity risks.
Holmes: The patient care benefits provided by increasingly connected medical devices have also introduced a downside, namely their inclusion in cyber attacks on entire facilities. Unfortunately, traditional IT solutions typically don’t identify these attacks, meaning biomeds must adopt health care-specific protections that monitor potential threats, remove the “noise” often found in older protections, and provide guided response actions to neutralize and recover from attacks. The Cynerio team introduced such a product with Attack Detection & Response nearly a year ago and continue to lead the charge in protecting medical devices against modern attacks.
Kane: Nessus scanning! Nessus is a remote security tool that scans networks for vulnerabilities. The scans can be applied to any operating system and return the exact vulnerabilities that need to be addressed.
Waters: Inventory remains the most important tool to aid in the security management.
westphal: Ordr is a connected device security platform that helps organizations see all devices connected to the network, know the potential vulnerabilities, and secure devices with vulnerability management workflows and automated policy. With Ordr, HTM teams can automate asset discovery and classification, improve accuracy of inventory tools, identify vulnerabilities and work across teams to address vulnerabilities, respond to active threats and proactively improve security.
Q: What are some cybersecurity features/options HTM professionals should look for when purchasing new medical equipment/devices?
DIMINO: Evaluate the sales proposal and incorporate contract language that aligns with your cybersecurity needs. Include language around the ability to install agents, patching, updates/upgrades, service level agreements (SLAs) and even installation requirements. Hold your vendors accountable, don’t accept insecure and outdated devices when the vendors are installing. Install agents (when applicable), perform vulnerability scans, and have your vendors setup your secure configuration requirements on devices before you accept for clinical use.
Grimes: When considering the acquisition of new medical devices and systems, health care facilities should require sellers to provide a relevant copy of the Manufacturer Disclosure Statement for Medical Device Security (MDS2). This document is based on a National Electrical Manufacturers Association (NEMA) standard and most medical device manufacturers produce a version for each device model they produce. The MDS2 provides information about a medical devices’ security features and vulnerabilities that can help health care facilities place and operate the device in a secure environment.
Holmes: When purchasing new devices HTM teams should consider both the device-level security as well as how to securely deploy the devices. A variety of checklists exist, but many Cynerio customers have noted that the recently updated (Nov. 2022) Medical Device Cybersecurity Regional Incident Preparedness and Response Playbook created by the FDA and MITRE provide helpful guidance for every part of device adoption from procurement to incident response.
Kane: Ultimately, your department’s purchasing ability is entirely dependent on your facility’s cybersecurity limits. At a government facility, we employ stricter cybersecurity measures than most private hospitals. Because of this I can’t speak to the latest and greatest cybersecurity options, but I can tell you that knowing the basics matters. Ideally, and many times realistically, what OS can you support? What about antivirus, external network connections, encryption, firewalls? Building a robust cybersecurity program starts with purchasing devices to meet your current infrastructure, and then growing the infrastructure to meet industry standards.
Waters: First, look for patchability and a commitment from the manufacturer to maintain the product. A system that is difficult to update or upgrade will be become “legacy” sooner. Secondly, make sure any integrations over the network are encrypted. There is a lot of patient data flowing in plain text throughout hospital networks. We need to get past that.
westphal: HTMs should look to vendors who are committed to providing and maintaining up-to-date details on the operating system and software components of the medical devices they sell. Knowing these details are essential to understanding the risk these devices present in your environment. Insights from vendors should be shared in the form of a comprehensive Software Build of Materials (SBOM) that can be used by tools to operationalize these insights. In addition, vendors should provide regular SBOM updates and communications about vulnerabilities, recalls and available patches/updates.
Q: What else do you think TechNation readers need to know about cybersecurity?
DIMINO: Explosive growth of IoMT devices will continue to lead to significant security challenges. HDOs will continue to experience attacks, and eventually patient safety will be compromised in a manner that draws worldwide attention. The problem cannot be solved in ad-hoc bits and pieces. Understandably, HTM alone can’t solve all the challenges, but in a collaborative effort with security/IT and building a medical device security program you can reduce the risk, likelihood and impact of an attack.
Grimes: TechNation readers should understand that effective cybersecurity in their organizations requires not only the efforts of CE/HTM professionals but also the collaboration between these professionals and other stakeholders including device users, IT security, facilities management, risk management, supply chain, manufacturers and the organization’s leadership. An effective cybersecurity risk management program will depend on each of these stakeholders being well informed and fully participating in the program in a cohesive and coordinated fashion.
Holmes: The harsh truth is that attackers may be evil, but they are not ignorant. Cyberattacks on health care continue to grow for simple reasons including lagging adoption of cybersecurity best practices, rapid introduction of insecure devices deployed in insecure manners, and increasing likelihood of paying ransoms to enable continued patient care. As long as the health care industry is seen as the easiest path to revenue, we will continue to see hundreds of successful ransomware attacks, tens of millions of patient records exposed and increasing headlines that erode patient confidence in their local facilities.
Kane: As cliché as it sounds, cybersecurity is an inherently dynamic field. Most of the work is preventative and you always hope it stays that way. However, when incidents do arise, and it’s almost inevitable they will, you want to flatten the impact curve as soon as possible. For better or worse HTM professionals are the subject matter experts for their own devices, so it’s up to each of us to assume this expertise in all forms – cybersecurity included.
Waters: As medical devices become more integrated, we need to think of them as parts of a system. The more effectively an HTM and IT department can work together the better they can protect the system as a whole while taking into account clinical impact and minimizing disruption to patient care.
westphal: Cybersecurity threats are continually evolving as are the tools and methods available to protect your environment. Protecting an organization cannot be done in silos or by any single team so it is important to leverage tools that help to bring together insights and teams in support of a whole hospital approach to security.




