By Garrett Seeley
The effects of quality documentation have always impressed me. A lot of techs would see this as tedious and, in truth, it can be. However, keeping adequate records is one main tasks of a healthcare technology management professional. This has become a bit of a double-edged sword when balancing workload and the need to document it. It is often hard to find the time. Regardless, it is important, not just in work orders and inventory, but also in networking. To illustrate, I would like to present a model that was given to me by a past shop manager. Before I begin, let me state that this it is an earlier model from before technologies such as Cisco ISE. We covered some of the possibilities of networking software in the Unified Threat Management (UTM) articles and it is superior to this technique. Please consider the following as a launching point; a beginning thought as to what to look for in complete networking documentation. This will give a starting point as to what to ask the UTM systems to provide.
When I was taught about networked device documentation, the presenter gave the following scenario: if there was an emergency, say a vulnerability in an operating system that required an immediate response from the HTM shop, how would anyone know what machines are affected? What if it was just a certain version of an operating system that is affected, would anyone know where those devices are? What if it was just a certain patch? For example, if this vulnerability only affected the Windows 10 Operating System, OS builds 1803 and earlier, and these devices must be unhooked from all networks immediately what inventory numbers are those units and where are they located? This is a hypothetical situation that illustrates exactly what was asked of people during a cyber-attack. In such a case, we may have to find and isolate vulnerabilities quickly. The challenge is, how do we do that? This scenario drives home the value of knowing what is on the network, what OS it has, and where it is physically located.
To help in these situations, use a list. This list can help serve as a guide regarding what to keep track of pertaining to networked medical devices. As best practices, every biomed should have access to something like this in their hospitals:
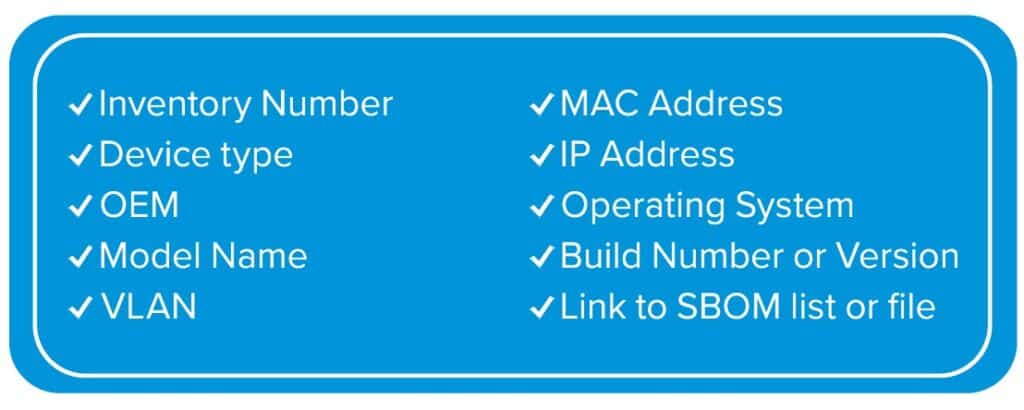
All hospitals have on site inventories, and therefore specific numbers for each machine. This is specific to each site in their work order clinical maintenance management system (CMMS). I find it important to describe what to look for by saying, for example, Ultrasound, GE, Logiq P9. This helps to know exactly what we are looking for. Sometimes a location, room number, or department can be added as an additional guide to find a unit. We really need to know the VLAN information. This can be a number, such as 101. It helps see how the network is segmented and will help if the device moves to another VLAN within the hospital (see articles on network subnetting). MAC and IP addresses, operating systems and build information are critical for assessing a vulnerability in a pinch. I suggest also having a SBOM link, if possible. We covered SBOM in a previous article; it is a list of software loaded on the device. This could be on the web, but it could be a PDF file in a local shared folder. This is a great item to be able to reference in a hurry as not all vulnerabilities are operating system related.
One of the main goals of this type of list is consistency and searchability, and this leads to another important concept. We have not covered this term before, but the term for database consistency is “normalization.” Frankly, there is a lot of information regarding normalization and how the problems with inconsistent language use can be avoided. Consider a computer’s a search function. If a user searches for my employer, the computer thinks the terms VA, Veterans Affairs, and Veterans Administration are all different things. To a person, they are all the same thing, even though the last one is the wrong term for the Veterans Affairs Healthcare System. This is an example of how a computer requires exactness whereas our minds think in terms of “it’s close enough.” Believe it or not, when referencing information, small details such as correct spelling are extremely important. Computers don’t think in terms of close enough. This effect is vastly important for searching through information. The act of fixing all these little inconsistencies in personal data entry is called normalization. For example, CPT and ICD10 codes are a normalization used in health care. We had to use such things because the inconsistencies of medical language use, statistically around 40%. That means the co-workers entering the same thing without cut and paste or some form of template to help will use different wording 4 out of 10 times. Therefore, have a uniform stated language to make the data easier to search in an emergency. This is not just useful for networking documentation, but consistent wording in work orders lends itself to easily quantifying our workday. This helps ensure that our work orders are consistent and easily searchable, and clear.
These are some basics of documentation for networked medical devices. Thankfully, there are companies that produce software to help, that is however, another article. Regardless of the method used, encourage HTM professionals to compile this information. “You’ll thank yourself later if you document now.” It’s a quote from myself written in my planner 25 years ago. It has become a personal motto of sorts. I use this as a personal reminder that we are paid to be meticulous. After all, when it comes to medical equipment, it is literally a matter of life and death. It can be a matter of litigation. In such a crisis, there is no substitute for adequate documentation.





